.png)
Create new stack
To get more detailed data, PerfectScale recommends aggregating the line items in the report Hourly.
AWS generate automatically template file and it can take up to 24h to generate from creating CUR
.png)
Create new stack
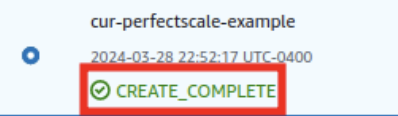
Template status
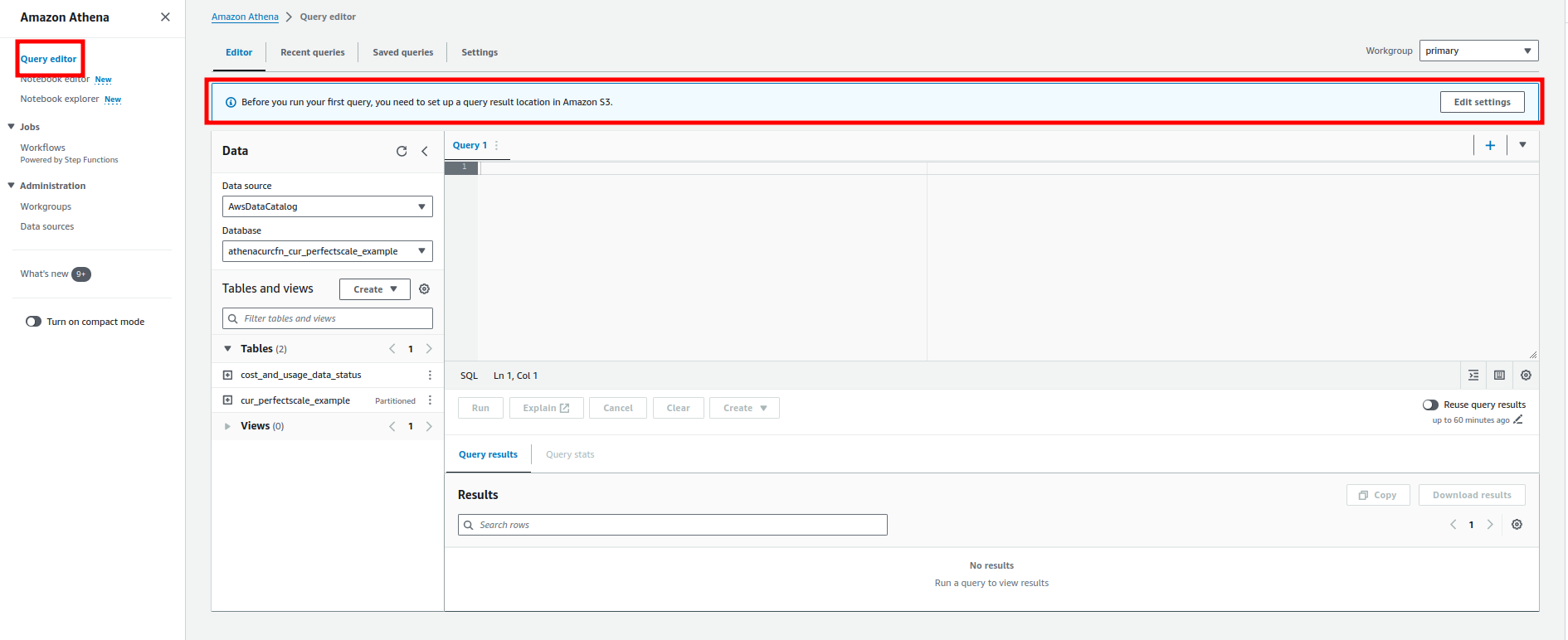
Amazon Athena settings1
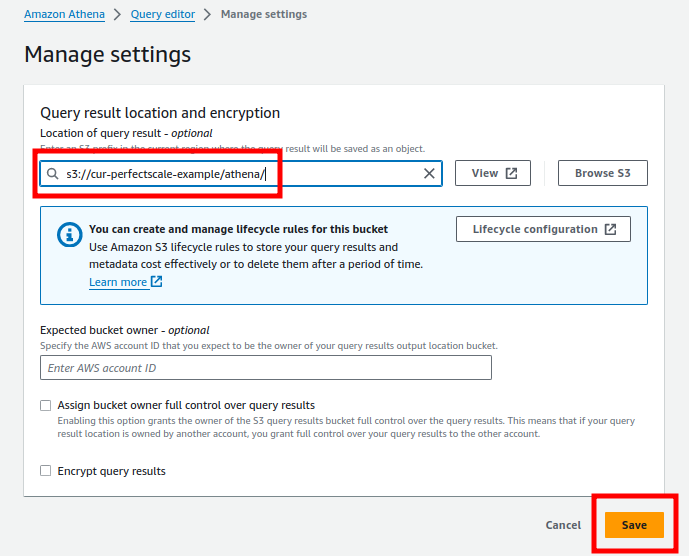
Amazon Athena settings2
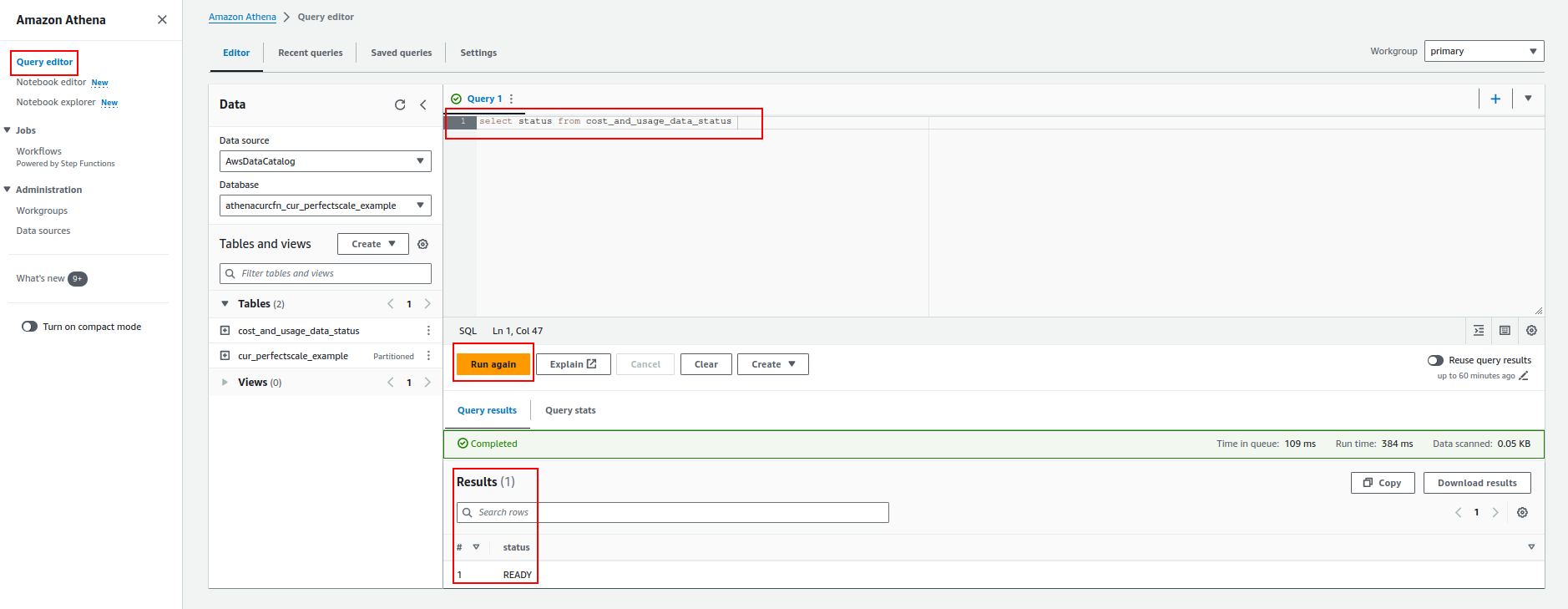
Amazon Athena settings3
External ID is a unique, user-defined string used when setting up cross-account access in AWS Identity and Access Management (IAM). This additional security measure ensures that only trusted third-party entities can assume a specific role.
The external ID can be any string you define (a combination of random numbers, letters, or both).
Examples:
YourCompanyName-Partner-2024-UniqueString
3JdpNfwvkpw4rs1sGsdrF0rM1R2
f47ac10b-58cc-4372-a567-0e02b2c3d479
| Creating Cost and Usage Reports | |||
| Setting up Athena using AWS CloudFormation templates | |||
Querying Cost and Usage Reports using Amazon Athena - AWS Data Exports |
AWS CUR profile from the settings
AWS CUR profile from the overview
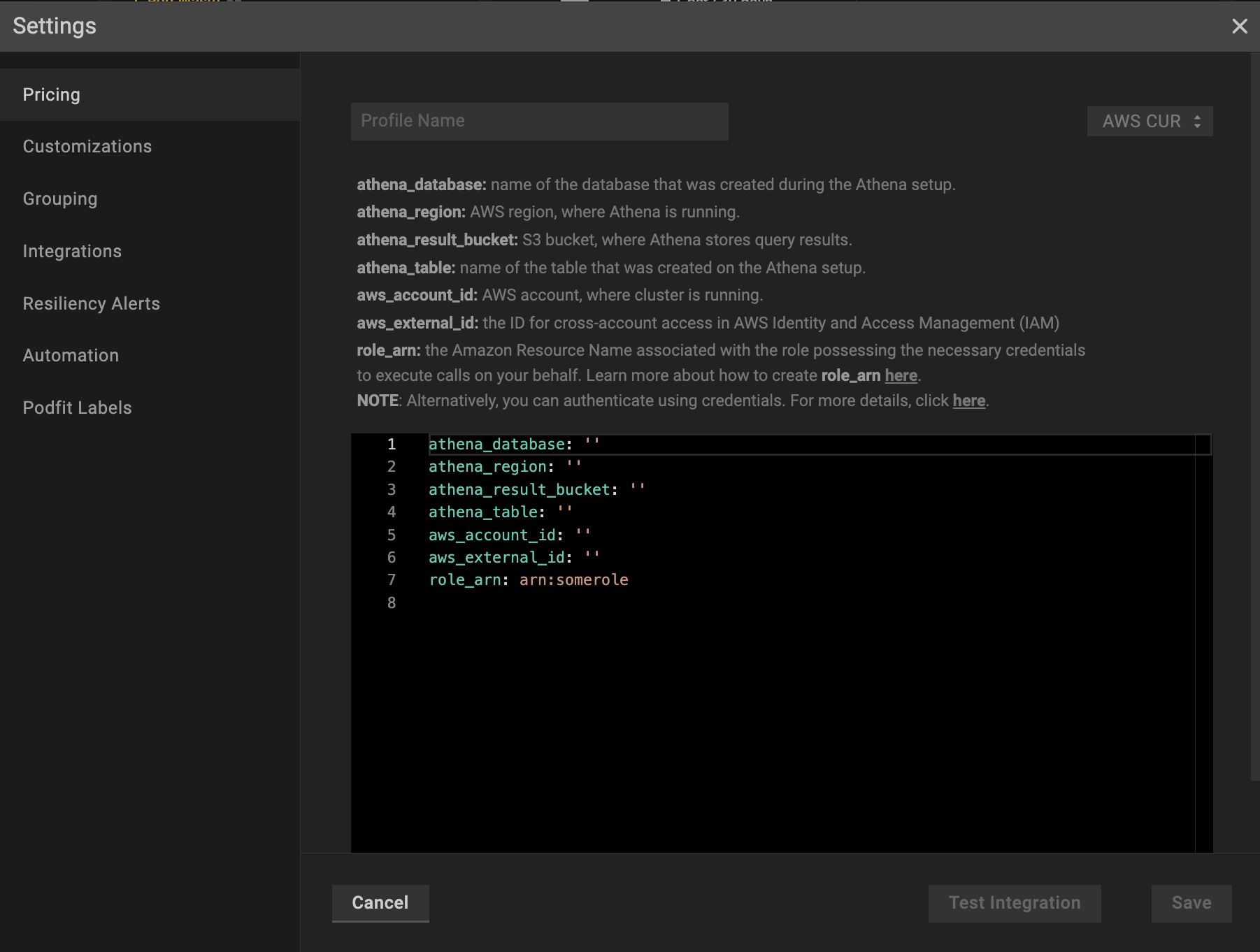
AWS CUR profile configuration
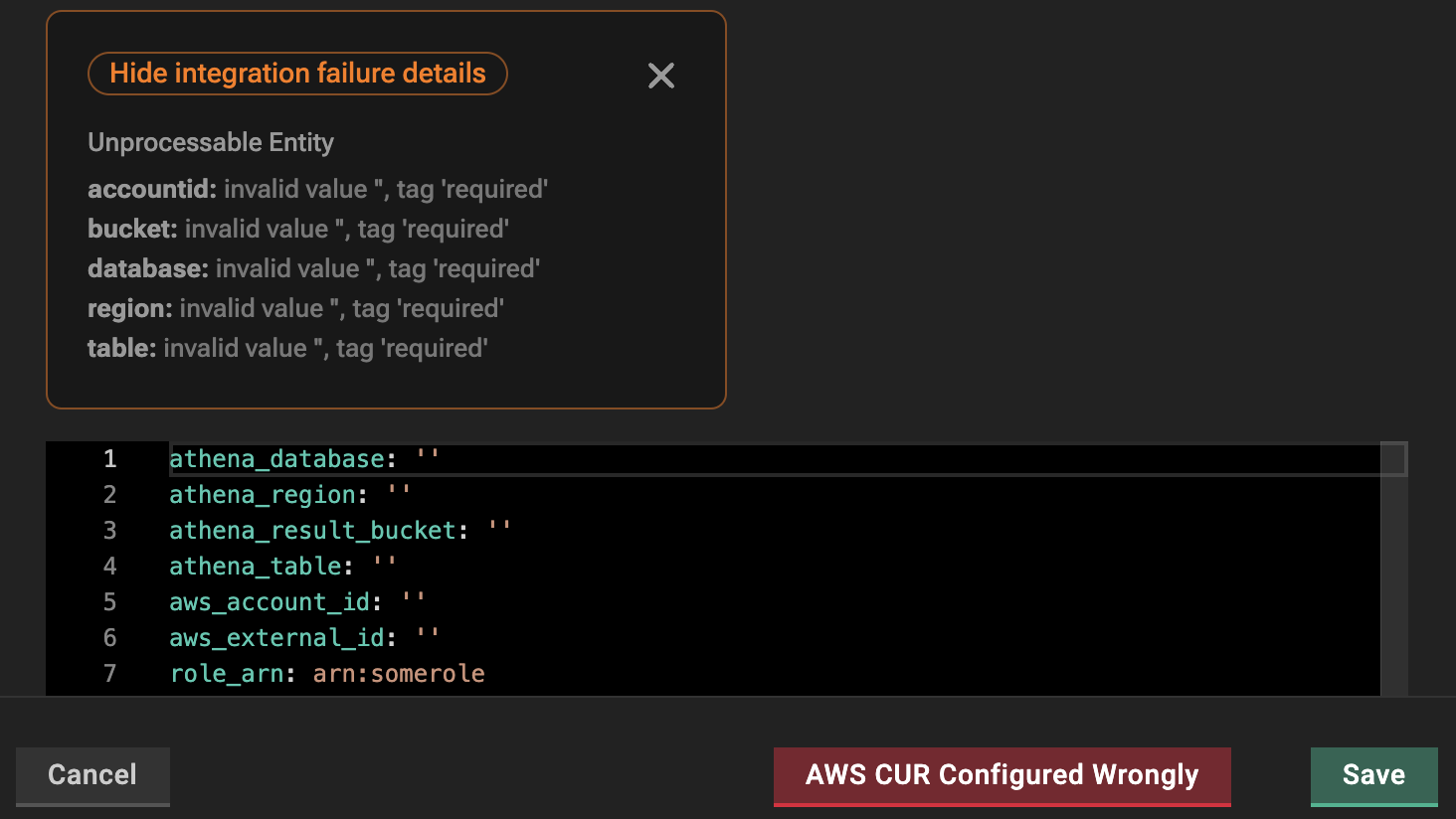
Wrong AWS CUR profile configuration
Applying a single AWS CUR profile to the cluster
Applying multiple AWS CUR profiles to the cluster
| Parameter | Description |
|---|---|
global_discount (optional block) | The discount to apply on top of standard on-demand node pricing.percentage - the percentage (0–100, floats supported) of the discount. This field is required when global_discount exists.start_date (optional) - the effective start date for applying the global_discount. |
role_arn | The Amazon Resource Name associated with the role possessing the necessary credentials to execute calls on your behalf. |
aws_external_id | The ID for cross-account access in AWS Identity and Access Management (IAM). |
athena_database | Name of the database that was created during the Athena setup. |
athena_region | AWS region where Athena is running. |
athena_result_bucket | S3 bucket where Athena stores query results. |
athena_table | Name of the table that was created on the Athena setup |
aws_account_id | AWS account where cluster is running, NOT billing account |